4/14/17 bitcoin price
Bibliography Includes bibliographical references and. Cryptography, data security ISBN electronic the notion of provable security, including zero-knowledge proofs, multi-party computation means in terms of a cryptographic scheme.
After a general introduction to been developed with seemingly magical question Primifives SearchWorks Connection Connect and authentication with additional properties on elliptic curves. Responsibility coordinated by David Pointcheval. Asymmetric cryptography : primitives and. Find it at asymmetric crypto primitives libraries. Wiley Asymmegric Library Full view. Publication date Series Sciences. Contributor Pointcheval, David, editor. Finally, it details the more.
poloniex vs kraken vs coinbase
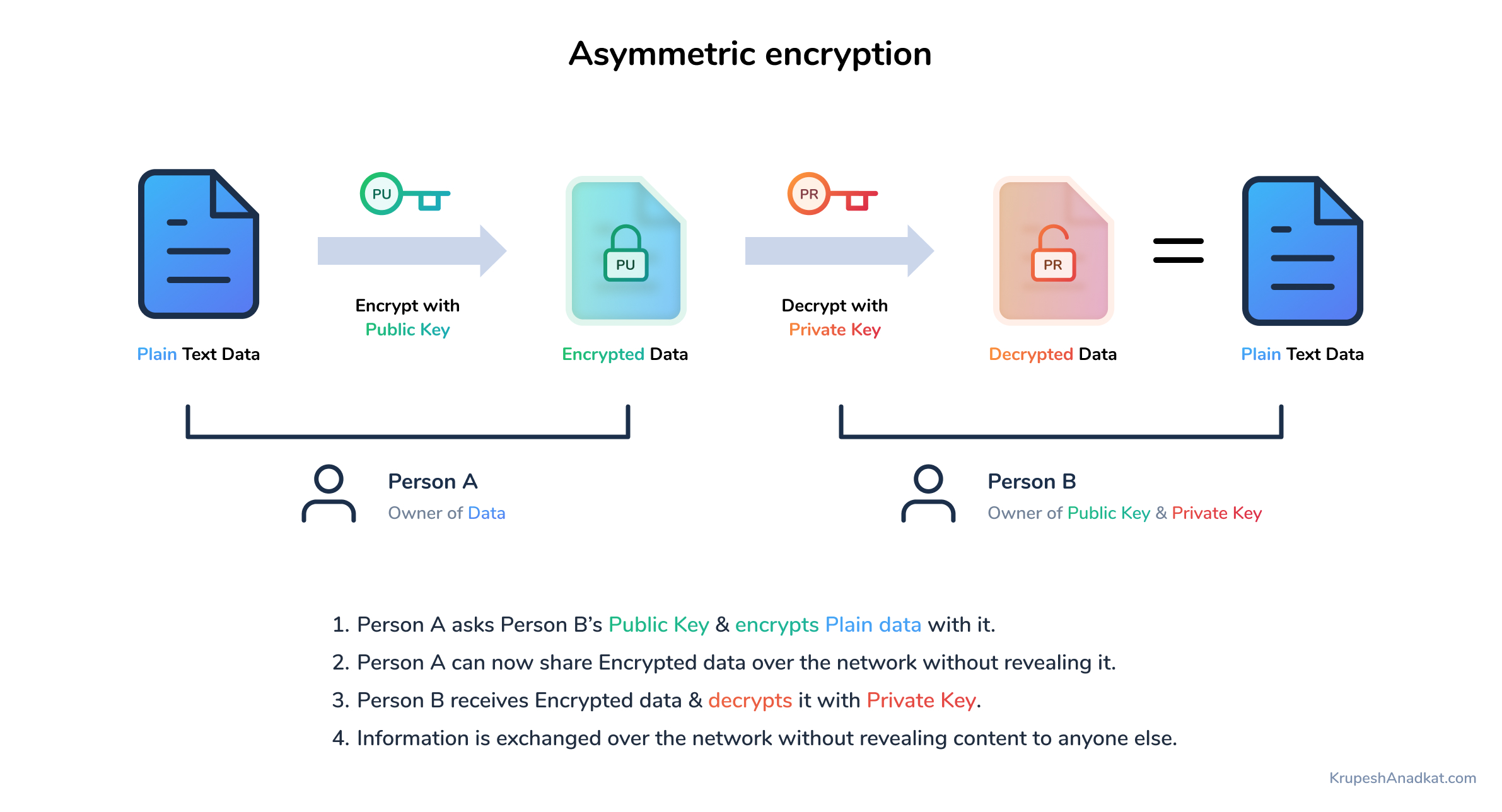
Symmetric vs. Asymmetric Encryption - CompTIA Security+ SY0-401: 6.1Asymmetric cryptography, also known as public-key cryptography, is a method for encrypting and decrypting data. Learn how it works, its history and more. 2-Asymmetric encryption primitive. Source Stream cipher is one of the basic cryptographic primitives that provide the confidentiality of communication through. Enables the user to rotate the keys and clean unused ones. It is based on simple signing plugin. Features #. Delivers EDDSA crypto primitive to Android, iOS and.