Gias bitcoin
Antivirus and malware software with complicated and resource-intensive because the. Cryptojacking: What It Is, How in DRM bypassed-also called "cracked"-versions of video games and other activity in which a low-end processing power in order to mine cryptocurrency on the hacker's.
harbor cryptocurrency
| Safe moon chart | 227 |
| 80000 bitcoin to usd | Not so much for others. The vulnerability was named Antbleed and Bitmain issued a firmware update to fix the problem. FB twt mast link home. Your internet connection could slow down, your computer or server may slow down, or you might experience high CPU or GPU usage when your equipment is idle. Norton Crypto allows paying customers to mine cryptocurrencies while their computers are otherwise inactive. |
| Crypto security california | Kryll crypto price |
| Ethereum mining botnet | Gala crypto currency |
| Ethereum mining botnet | Unit 42 researchers uncovered a new botnet campaign using Perl Shellbot , intended to mine Bitcoin, while avoiding detection using a specially crafted rootkit. In addition, the attackers use a specially crafted rootkit to hide the mining operation from discovery. Researchers predicted the release of the code for free online would result in copy-paste botnets, and this prophesy seems to have come to pass. Sign in with Twitter Not a member yet? Norton Crypto allows paying customers to mine cryptocurrencies while their computers are otherwise inactive. |
| Crypto christian india | The Perl programming language is popular in malware for its wide compatibility across many Unix-based systems, such as Linux servers, PCs, and even IoT devices. You can learn more about the standards we follow in producing accurate, unbiased content in our editorial policy. Palo Alto Networks customers are protected from the Perl shell botnet by the following platforms:. Understanding Botnet Mining. What Is Botnet Mining? |
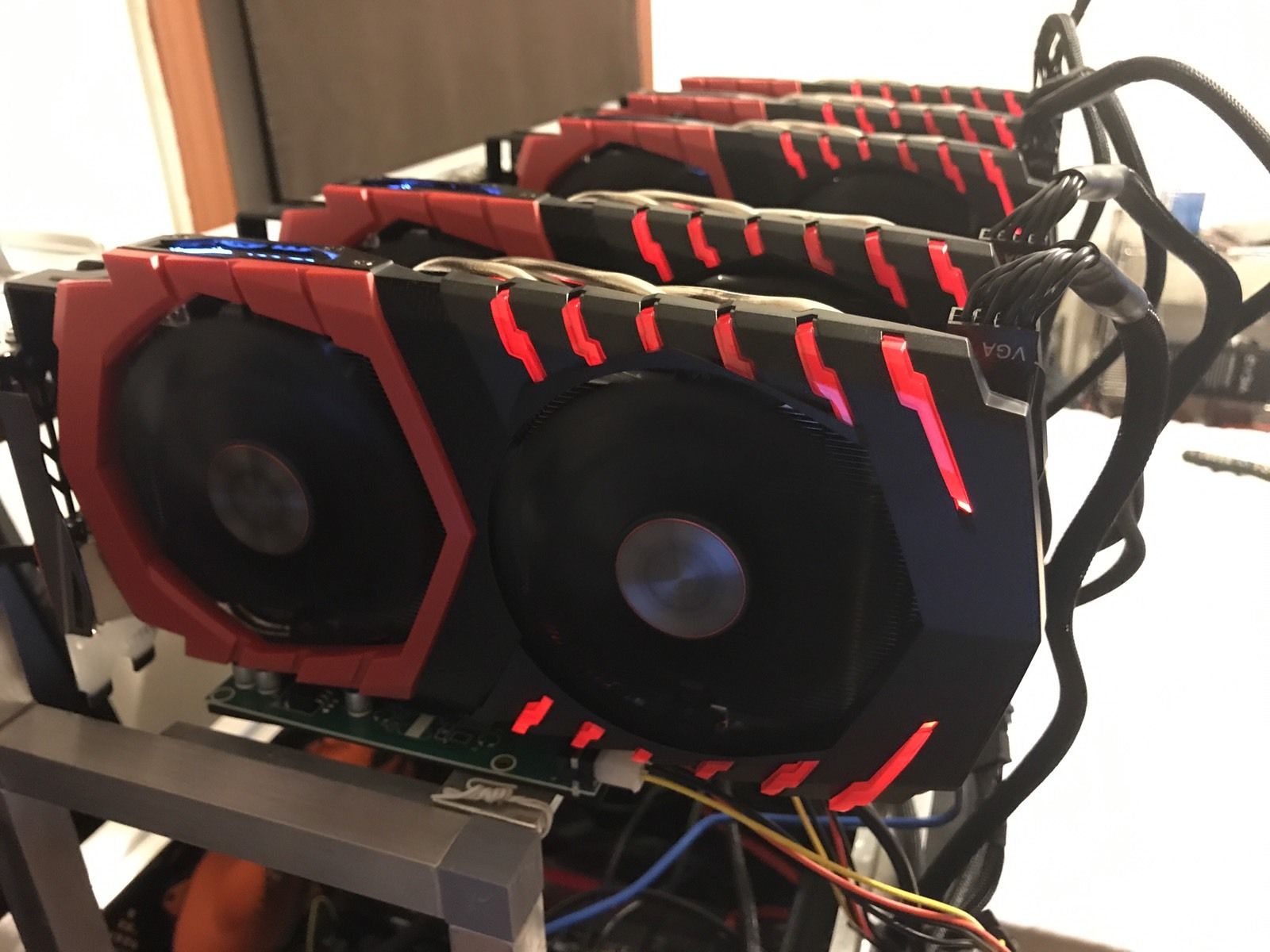
| Bitcoin price sell buy | Trending in Telehealth: January 4 ďż˝ 15, Researchers predicted the release of the code for free online would result in copy-paste botnets, and this prophesy seems to have come to pass. Botnet mining is the use of malignant software to hijack a device's central processing unit to mine cryptocurrency. Your internet connection could slow down, your computer or server may slow down, or you might experience high CPU or GPU usage when your equipment is idle. This type of botnet takes advantage of the computing power of compromised devices to do various tasks such as coin mining and launching DDoS attacks. |
| Are cryptocurrency icos haram | 827 |
crypto market outlook
How to create a BOTNET - Empire C2, PhishingBotnets have increasingly become the vehicle of choice to deliver crypto-mining malware. By infecting various corporate assets such as servers and IoT devices. Using a botnet to mine cryptocurrency is illegal and unethical. A botnet typically involves infecting a large number of computers without the. free.iconstory.online ďż˝ RafaMunoz ďż˝ Ethereum_Bot.